Big Data PhD Topics
Big Data PhD Topics grant scientific royal farmland to sowing your knowledge seeds with the best fertilizer of goal for harvest continuous achievements. We are experts of experts in big data research to help scholars from research topic selection to final viva voce. Today, mass of the PhD scholars face more troubles in thesis preparation part. Thesis preparation part is the complex section in PhD research stages. Due to this, we establish thesis preparation service for PhD academicians to provide comprehensive support in their research thesis preparation part. If you eager to prepare your thesis with our guidance, you can get in touch with us today. We are willing to guide you forever.
Big Data PhD Topics
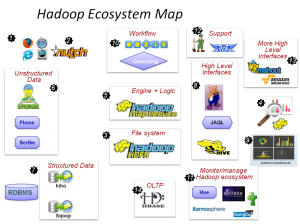
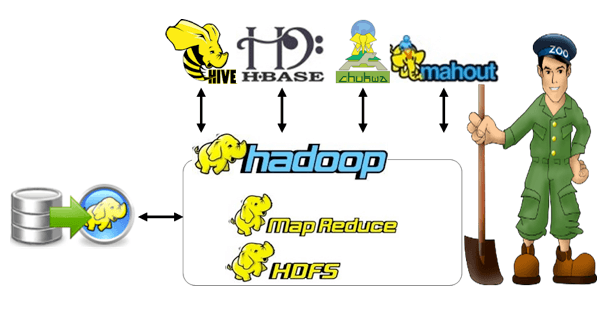
Big Data PhD Topics is our outstanding service to give world-shaking research topics for PhD scholars to choose excellent topics with our expert’s guidance and support. We are only working for students and research scholars with the vision of help scholars by our innovative and genius ideas. We give premier training for scholars in big data including scalable storage systems, large scale data analytics, parallel programming techniques, massive big data processing, big data models, stream data processing, Hadoop programming, privacy preserving big data analytics etc.
Let’s look a brief information about Big Data Security that part of the Big Data,
By the very huge size of data coming from various devices and computers, Big Data needs Big Security because the data is vulnerable to cyber threats. The most unsolvable ones are threat filtering, alerting, activity monitoring and access control.
All types of data may lack of Big Data Security. Here’s why,
- A data change from Terabytes to Petabytes is so large. This leads to multiple vulnerabilities
- Data owner does not regularly update security. If it not perfectly performing, it leads to a data loss problem
- Can’t to process unstructured data analytical tools while using security software
- Security tools may not monitor or alert when suspicious access was taken by the Big Data Administrators
Security Technologies to add Big Data Security:
- Encryption Tools
- User Access Control
- Centralized Key Management
- Physical Security Systems
- Token based Authentication
- Unified Authorization Framework
- Improved Security in HBase
- Intrusion Detection and Prevention Systems
There are number of research questions are raised from world’s many countries. The common security questions are:
- How the Hadoop integrate with Advanced Security Tools?
- Which encryption tool you use to encrypt data in transit?
- How to implement Role based Access Control/Attribute Based Access control?
- How to find who is a legitimate user to access, change or terminate the process?
- How to find how much the data in secure?
- Which algorithm/tool can be used for user’s authentication and data owner?
- Which type of key management (Distributed/Central) is suitable for massive data processing?
- Which one is a suitable approach for Intrusion Detection?
Most of these questions are not concentrated currently because these are the challenging issues which are not overcomes by any approaches. Our team of experts has 10+ years of experience who can guide you from your beginning of research. Why you still thinking? Take a mobile, just ring of us. We back to you in few seconds. Let’s see some interested Big Data PhD Topics,
- Create Homogeneous Magnetic Catalog Spanning Four Solar Using Limited Human Supervision and Automatic Detection
- Classification of Document Over Wildcard Training and Character Embedding Based on Image
- Popularity Aware Cost Effective replication Strategy in Cloud Storage for High Data Durability
- Big Data Analytics Application for Automated CT Image Quality Estimation
- Identify Machine Learning in Human Hut Micro-biome Protein Family Abundance to Identify Major Shifts in Disease
- Provenance Aware Spatial Temporal Architectural Paradigm for Massive Data Analysis and Integration
- Network Topology and Memory Hierarchy Exploration Across Scientific Applications for Run Time AMR Data Sharing
- Content Based Recommendation Using Natural Language Processing Techniques for Podcast Audio Items
- Genome Sequences and Optimization of FHE Bootstrapping by Privacy Preserving String
- MDL Change Statistics for Detect Data Stream Gradual Changes
- Location Specific Santa Ana Conditions Detection Using a Scalable Mechanism
- Customized Cooperative Resource Provisioning in Clouds for High Resource Utilization
- Frequent Pattern Mining and Dynamic Support Values for Detect Social Network Streams Event
- Temporal Association Rules in residential Homes for Electrical Activity Detection
- Cloud Operation Management Using Fine-Grained Emerging Graph Processing Power Analysis